
Hey folks – well, 2020 has turned out to be an interesting year in so many ways. It’s hard to believe that when I wrote my last column, way back in March (a whole six months ago!), I had just returned from what would turn out to be my last trip of the year so far. That’s six months that I’ve been home – the longest I have ever been home at one stretch in almost 30 years. If you’re a praying sort, you might offer up some kind words for my wife, she’s definitely exhibited the patience of a saint as I learn to deal with staying in the same place for so long!
That said, there have been some good things come out of not being on the road living from a suitcase for half of the year – one of those things has been our Transmission Talk Tuesday (TTT) round-table discussions. At the moment, we’re planning to keep those going through the rest of the year, and I’m working as hard as I can at keeping them both informative and non-sales oriented. If you have any ideas for a topic that you would like to see in a future TTT, contact me and I’ll see what I can do!
Our latest TTT session was on IT Security – a topic that broadcasters, and a lot of folks really, just aren’t that sure how to tackle. Obviously, the solution can be as complex, or as simple, as your infrastructure. If you’re an all analog facility with very little computerized stuff, there might not be a lot that needs to be done. If you’re a networked AoIP facility with infrastructure in many different locations and lots of connected subnets, the task might be a bit more daunting. It was great to have Wayne Pecena, the president of the Society of Broadcast Engineers, on board for this session, Wayne has a way of explaining things that even I can understand!
During our discussion, I’d mentioned a situation we had recently where somebody got an email that looked quite legitimate, clicked a link or attachment – and promptly sent a phishing email to everybody in their address book, including several of our customers. If you got one of those, I apologize. Our IT Manager spent massive hours reaching out to anybody involved and taking steps to try to prevent a repeat occurrence… tightening up email filters, creating some IT policies and doing some training in general to raise awareness.
This is the weak link in the best IT security – the social engineering. On that topic, Sean Mattingly, of Woof Boom Radio in Muncie, IN, sent me an email of tech tips that he sent out to do something similar. With his permission, I’m going to share it with you – because I’ve seen a few emails where I was convinced they were real, right up until I hovered over the “Click here to reset your password” link and saw the real URL. Without further ado, here are Sean’s tips:
SCENARIO:
You get a phone call. “How many computers do you have?” and “What kind of servers do you operate?”. The correct answer is “We don’t talk about our IT infrastructure”.
SCENARIO:
The boss asks you via email to pick up some gift cards. His signature and title appears at the bottom, a little shorter than usual. Or he wants you to reply with your cell number. The message does not come from his address. It is not him. There are scammers that monitor our main company website and try to trick employees into buying things. The scammers are in China, in Russian Federation, in Netherlands, etc.
Sometimes they’re after the codes on gift cards so they can redeem them. Other times they get pennies from their scammer bosses if they can harvest some cell numbers and sell them to telemarketer scammers.
SCENARIO:
Someone you know sends you an email attachment, a ZIP file with a “hurry” message. You don’t need it. You don’t want to open it. If you hover the cursor over the sender’s name, you can see it doesn’t even come from the person’s real email address. In webmail, mark that as Spam.
SCENARIO:
You’re opening an email attachment. The antivirus program is warning that it could be a dangerous attachment. Then it warns you that it HAS quarantined a file. This is an exceptional situation that still may have caused a data-stealing program to run on that computer.
Notify IT in your market immediately. The computer will have to be scanned THAT DAY and the offending message will be analyzed by IT Dept to see if it can be blocked to protect other users whom may receive a duplicate copy of it.
SCENARIO:
Your Firefox browser prompts “Do you want to install this browser add-on?” NO!
Your Chrome browser prompts “Do you want to install this extension for maps, or search protector, or coupons, or TV shows, or video downloader, or the ASK Toolbar?” NO!
These browser add-ons and extensions are vulnerabilities, often letting unknown companies spy on your computer use. Some of these browser customizations redirect your browser to altered search results or fake websites which look like the real websites. Some steal your browser cache (the words you saw on the screen recently) so they can read your webmail later.
What to do if you encounter a tricky computer situation:
Don’t let it run, don’t open it, don’t just hit “OK” messages without reading all the prompts.
SCENARIO:
You get a call. “We’re computer support and we need to connect to your computer for X reason.” NO!
SCENARIO:
You have a lot of apps on your mobile device. Most have access to your contacts, your location, and the files on your device. Read the EULA agreement when installing any apps. Most are very loose with permissions. If you have company email on that device, you have an obligation to keep it secure. Consider uninstalling all unnecessary apps for better data security.
All excellent tips, thanks very much for sharing, Sean!
As I mentioned, I’m starting to see the phishing emails coming in without the terrible grammar. The bad guys are getting better at what they do, so it’s important to be more aware.
One other thing I tell folks – if you have your laptop set up to go to sleep mode when closed, then if you do think you’ve got something nasty, close it immediately. Then call IT, so they can come take a look. It may be too late by that point – but it may also help to mitigate the damage, depending on the situation.
Another obvious tip – any USB stick that hasn’t just been scanned and verified clean should be treated as infected. If you need to transfer files, show prep or whatever, from one machine to another, I’m a big fan of OneDrive, DropBox, Box, etc.
 Off the topic of IT and into the hardware world, I’ve had a few folks send me pictures of various site-related things that I thought I’d share starting with this lovely grounding photo, provided by Eric Scace.
Off the topic of IT and into the hardware world, I’ve had a few folks send me pictures of various site-related things that I thought I’d share starting with this lovely grounding photo, provided by Eric Scace.
Who ever thought that TyRaps could be used to secure grounds? There’s not enough Noalox in the world.
 Eric also sent this one – I’ve seen vice grips used to connect a feedline to an AM antenna, but I don’t recall ever seeing them in the ground system before.
Eric also sent this one – I’ve seen vice grips used to connect a feedline to an AM antenna, but I don’t recall ever seeing them in the ground system before.
Seems like an expensive solution to something that could be resolved with a foot of solder and a blowtorch! Again, thanks to Eric Scace for these.
A couple more from Brett Erieg, of South Carolina ETV and Public Radio – sometimes you just KNOW what the problem is…
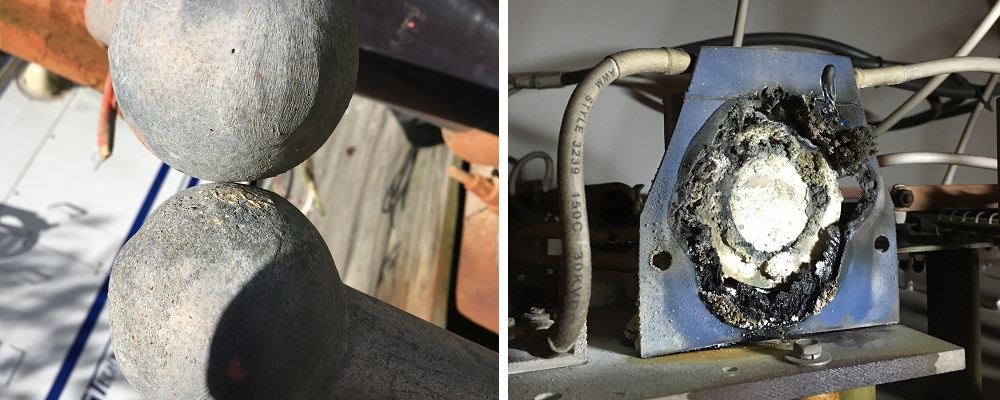
I can practically smell that photo! Thanks, Brett – I’ve got your other photos too, and they’ll probably show up in a future article.
On that note, wash your hands, folks, let’s all take care out there and I’ll see you next time – until then, be safe and happy engineering!
Jeff
Jeff Welton, has worked with Nautel for 30+ years. He is currently the Nautel Sales Manager for U.S. Central Region but previously he spent 16.5 years as a Nautel Customer Service Technician. A regular speaker and contributor on broadcast engineering, Jeff has been recognized with the following awards: 2020 NAB Radio Engineering Achievement Award; 2019 APRE Engineering Achievement Award; and 2018 SBE Educator of the Year Award.
Submissions for this Tips ‘n Tricks column are encouraged and if published you’ll receive a Nautel T-shirt. Submissions should be typed and emailed, with high resolution photos, to info@nautel.com using the subject line Tips ‘n Tricks.

